Safeguard your entire organisation with the industry’s first eXtended Detection and Response (XDR) platform
Security teams are inundated with inaccurate, incomplete alerts. Today’s siloed security tools force analysts to pivot from console to console to piece together investigative clues, resulting in painfully slow investigations and missed attacks. Even though they’ve deployed countless tools, teams still lack the enterprise-wide visibility and deep analytics needed to find threats. Faced with a shortage of security professionals, teams must simplify operations.
Cortex SDR
ML-powered threat detection
- Get an edge on attackers with patented behavioural analytics. Using machine learning, Cortex XDR continuously profiles endpoint, network and user behavior to uncover the stealthiest attacks.
Next-generation antivirus
- Block malware, exploits and fileless attacks with the industry’s most comprehensive endpoint security stack. Our lightweight agent stops threats by combining AI-driven local and cloud-based analysis.
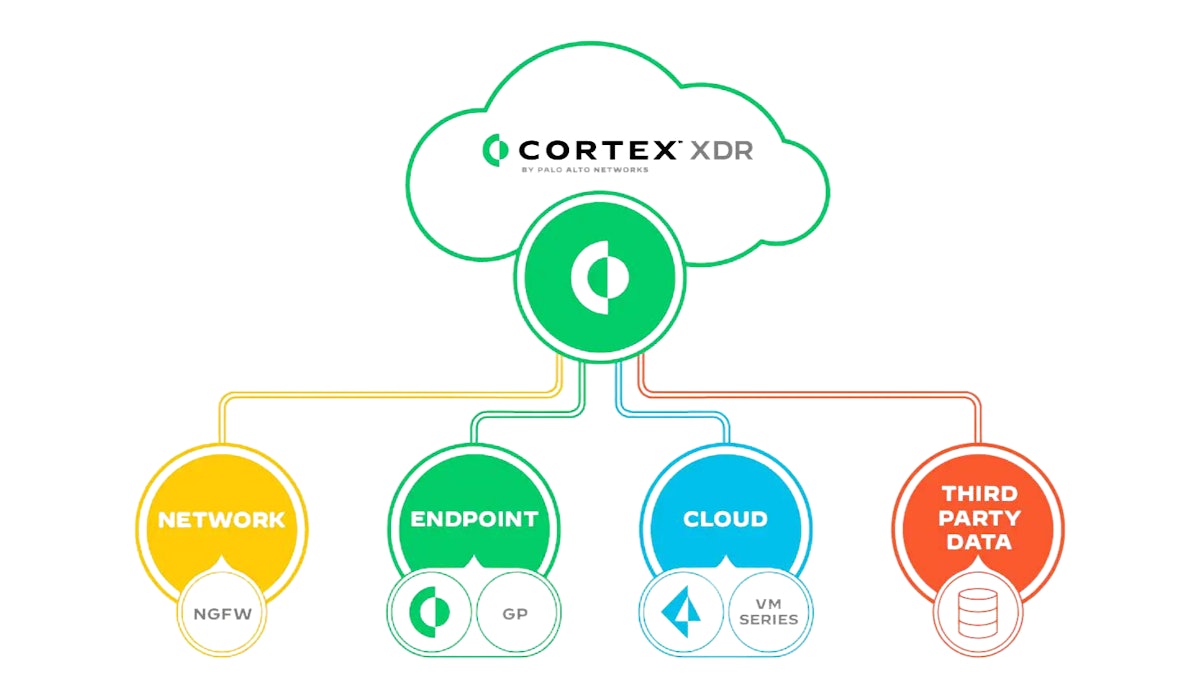
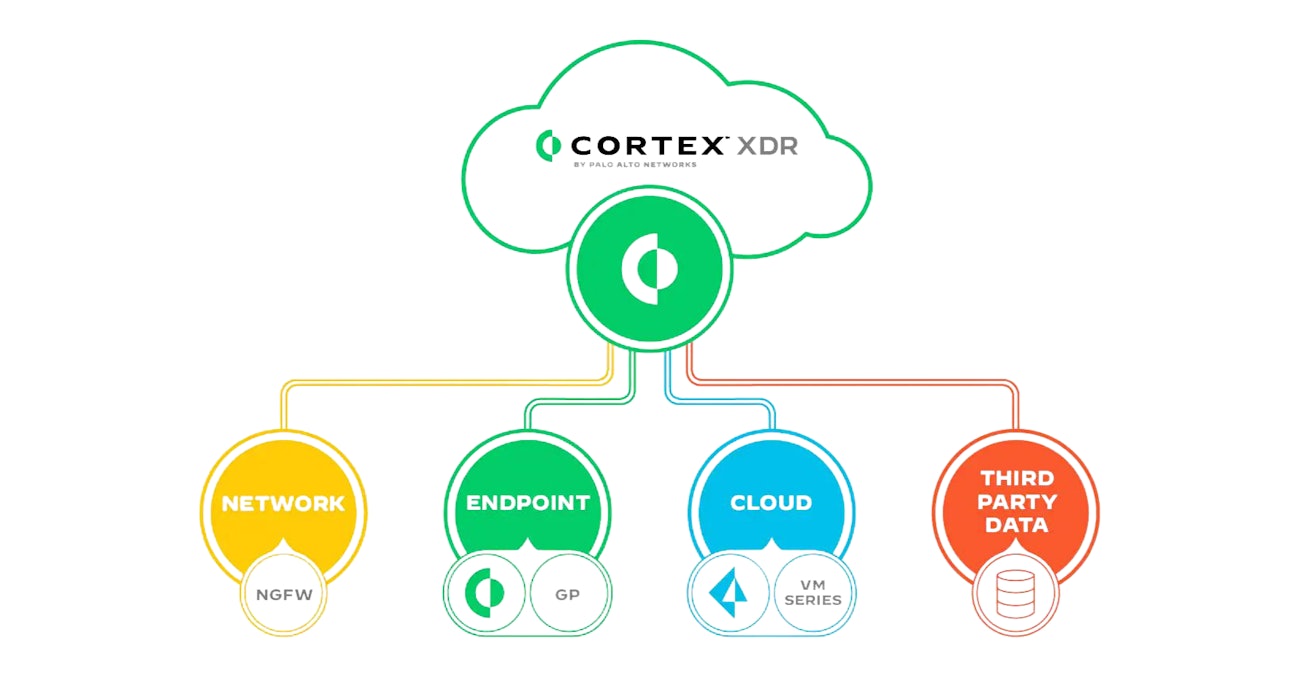
Enterprise-wide visibility
- Find every threat and eliminate blind spots by integrating data from across your environment.
Powerful endpoint protection
- Safeguard endpoint data and address compliance requirements with host firewall, disk encryption and USB device control.
Automated root cause analysis
- Analyse alerts from any source with a single click to instantly understand the root cause and sequence of events.
Incident management
- Investigate at lightning speed by intelligently grouping related alerts into incidents to get a complete picture of each attack.
Managed threat hunting
- Get with the industry’s first threat hunting service that operates on endpoint, network and cloud data to uncover every threat.
Ransomware protection
- Stop the exploits that lead to ransomware infection, block malicious files, and identify malicious behaviour to shut down attacks.
Coordinated response
- Swiftly block malware, isolate endpoints, execute scripts or sweep across your entire environment to contain threats. Cortex XDR offers flexible response options that span your entire infrastructure.
Business benefits
- Detect advanced attacks with analytics
- Uncover threats with AI, behavioral analytics, and custom detection rules.
- Reduce alerts by 98%
- Avoid alert fatigue with a game-changing unified incident engine that intelligently groups related alerts.
- Investigate eight times faster
- Verify threats quickly by getting a complete picture of attacks with root cause analysis.
- Stop attacks without degrading performance
- Obtain the most effective endpoint protection available with a lightweight agent.
- Maximise ROI
- Use existing infrastructure for data collection and control to lower costs by 44%.
- Eradicate threats without business disruption
- Shut down attacks with surgical precision while avoiding user or system downtime with Live Terminal.
- Increase SOC productivity
- Consolidate endpoint security policy management and monitoring, investigation, and response across your network, endpoint, and cloud environments in one console
- Supercharge your security team
- Disrupt every stage of an attack by detecting indicators of compromise (IOCs) and anomalous behavior as well as prioritising analysis with incident scoring.
- Gain visibility across network, endpoint, and cloud data
- Collect and correlate data from Palo Alto Networks and third-party tools to detect, triage, investigate, hunt, and respond to threats.
- Eliminate advanced threats
- Protect your network against malicious insiders, policy violations, external threats, ransomware, fileless and memory-only attacks, and advanced zero-day malware
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Zoeterwoude is ready to assist you.